Page 1 of 1
Active directory connection
Posted: 2018/09/23 12:59:21
by robertshatty
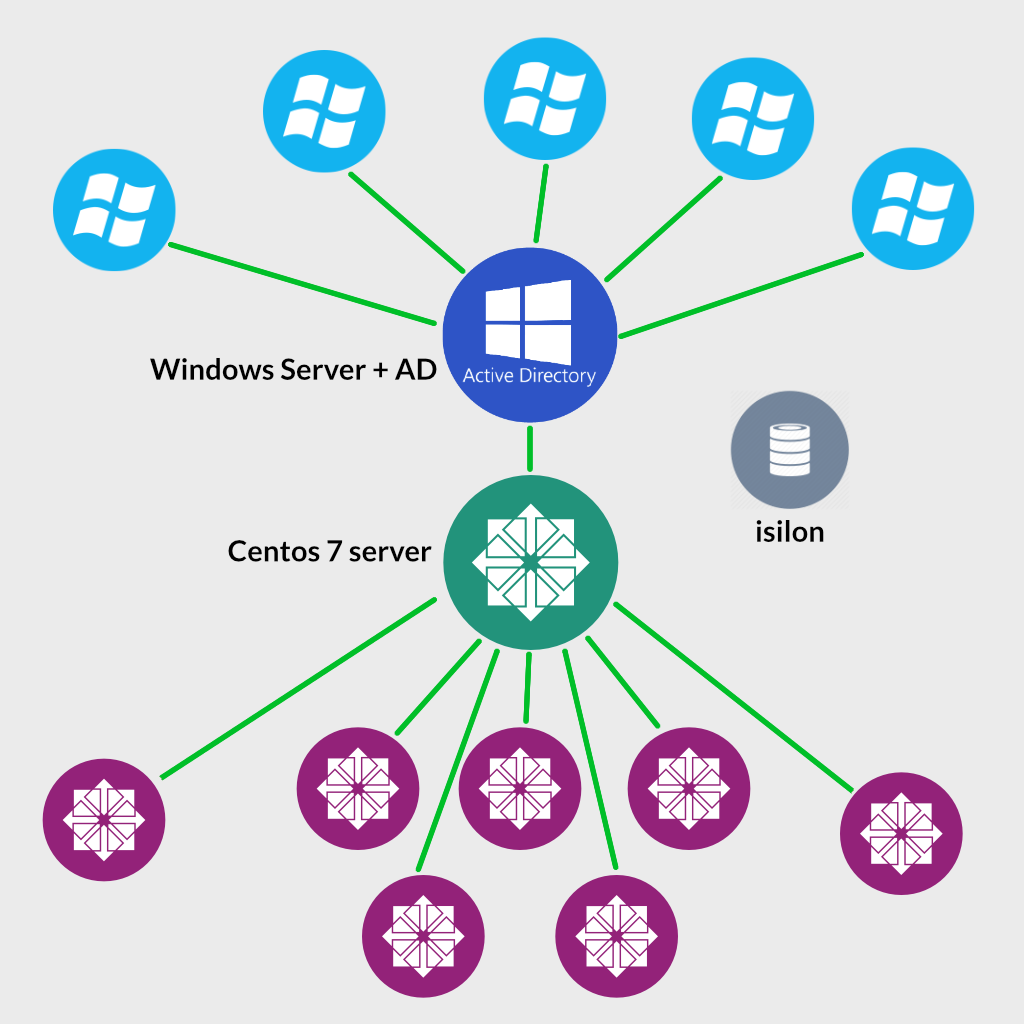
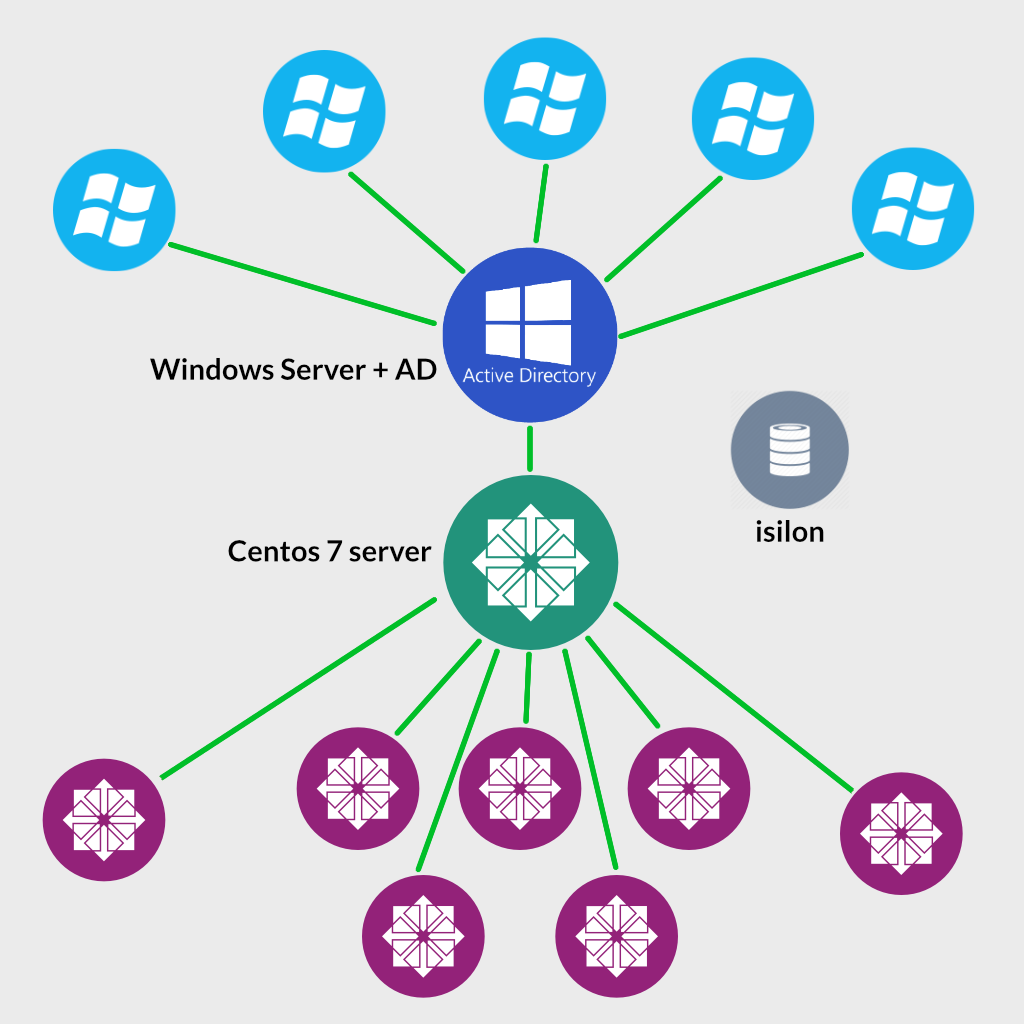
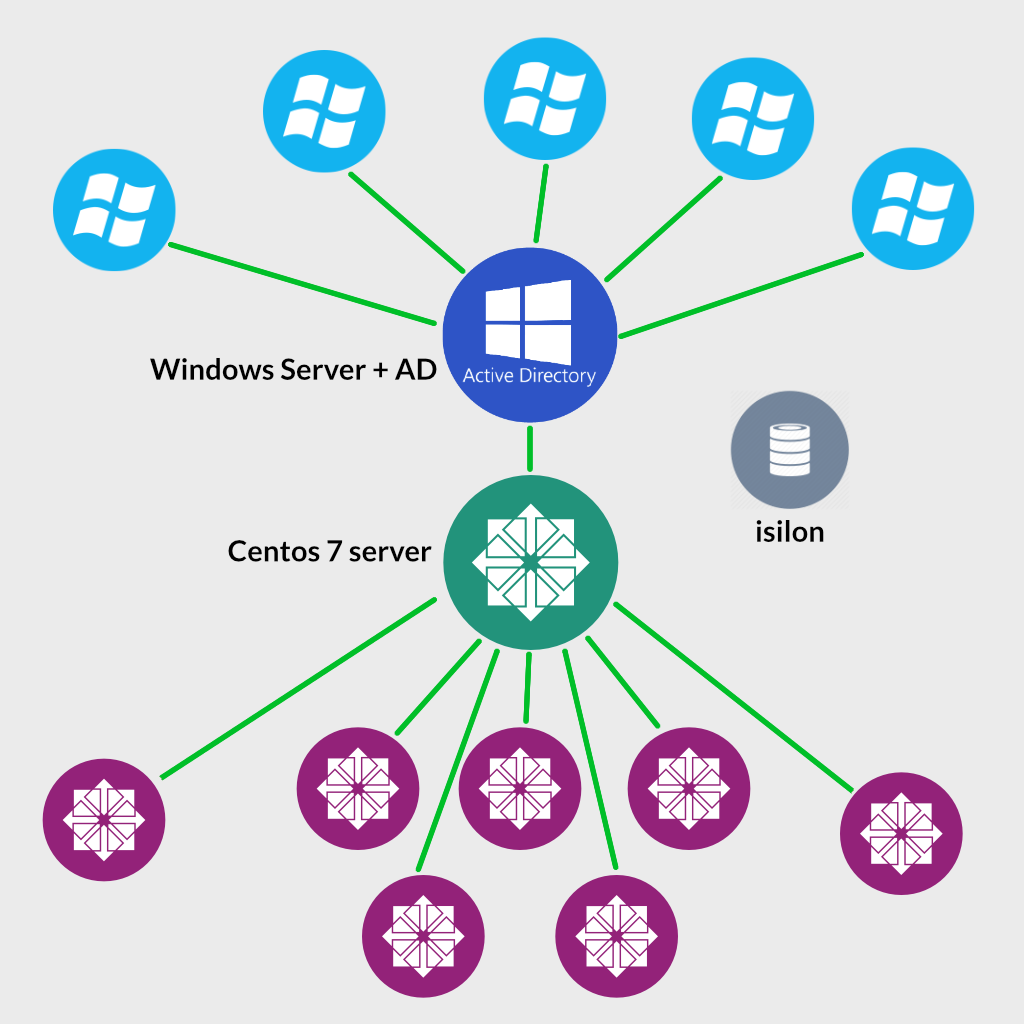
Hello, I'm looking for proper guidance on how to join centos 7 clients & centos 7 server to windows active directory ? I want to use user authentication & groups data from active directory on centos system. please see below image and tell me do i need to join only centos server to active directory or every centos clients also needs to join separately. ??
Thank you
Re: Active directory connection
Posted: 2018/09/23 16:14:06
by TrevorH
Re: Active directory connection
Posted: 2018/09/24 03:31:18
by robertshatty
This is what i tried, And got few question. Do i really need to join both windbind & sssd way ??
how to change home directory path to server (to make roaming profile)
how to remove suffix from userID (user.name instead of
user.name@example.com) ?
how to use active directory groups in centos ?? do i need to remap ??
Code: Select all
ping EXAMPLE.com
# DISABLE AND STOP FIREWALL
systemctl disable firewalld && systemctl stop firewalld
# INSTALL REQUIRED PACKAGES
yum -y install realmd
yum -y install samba samba-winbind samba-winbind-clients samba-winbind-krb5-locator
yum -y install ntp ntpdate
yum -y install sssd
yum -y install oddjob oddjob-mkhomedir
yum -y install authconfig-tui
yum -y install krb5-workstation
yum -y install openldap openldap-clients
yum install -y adcli
#-------------------------------------------------------------------------------------------------
# WINBIND
# NTP services get proper time sync from a domain controller:
systemctl enable ntpd && systemctl stop ntpd && ntpdate EXAMPLE.com && systemctl start ntpd
systemctl enable winbind && systemctl start winbind
# JOIN ACTIVE DIRECTORY SERVER
authconfig-tui
# >>> Go with following options
use winbind,
use shadow passwords
use winbind authentication
local authorization is sufficient
ads
/bin/bash
domain: EXAMPLE
domain controllers: ad.EXAMPLE.com
ADS realm: EXAMPLE.COM
(JOIN DOMAIN)
net ads testjoin
#Join is OK
realm list
EXAMPLE.com
type: kerberos
realm-name: EXAMPLE.COM
domain-name: EXAMPLE.com
configured: kerberos-member
server-software: active-directory
client-software: winbind
required-package: oddjob-mkhomedir
required-package: oddjob
required-package: samba-winbind-clients
required-package: samba-winbind
required-package: samba-common-tools
login-formats: EXAMPLE\%U
login-policy: allow-any-login
# EDIT THESE FILES
gedit /etc/krb5.conf
gedit /etc/samba/smb.conf
# RESTART SAMBA AND WINBIND SERVICES
systemctl restart smb.service && systemctl restart nmb.service && systemctl restart winbind
# RESTART SERVER (VERY IMPORTANT)
reboot
# AFTER REBOOT CKECK ALL REQUIRED SERVICES RUNNING FINE
systemctl status smb.service && systemctl status nmb.service && systemctl status winbind
# TO SEE THE LIST OF ACTIVE DIRECTORY USERS AND GROUPS IN CENTOS
wbinfo -u
wbinfo -g
# -----------------------------------------------------------------------------------------
# SSSD
realm leave example.com
realm join --user=administrator example.com
realm list
EXAMPLE.com
type: kerberos
realm-name: EXAMPLE.COM
domain-name: example.com
configured: kerberos-member
server-software: active-directory
client-software: sssd
required-package: oddjob-mkhomedir
required-package: sssd
required-package: adcli
required-package: samba-common-tools
login-formats: %U@example.com
login-policy: allow-any-login
Code: Select all
includedir /etc/krb5.conf.d/
includedir /var/lib/sss/pubconf/krb5.include.d/
[logging]
default = FILE:/var/log/krb5libs.log
kdc = FILE:/var/log/krb5kdc.log
admin_server = FILE:/var/log/kadmind.log
[libdefaults]
dns_lookup_realm = false
ticket_lifetime = 24h
renew_lifetime = 7d
forwardable = true
rdns = false
default_ccache_name = KEYRING:persistent:%{uid}
default_realm = EXAMPLE.COM
dns_lookup_kdc = true
[realms]
EXAMPLE.COM = {
kdc = ad.example.com
}
[domain_realm]
example.com = EXAMPLE.COM
.example.com = EXAMPLE.COM
Code: Select all
[global]
workgroup = example
password server = ad.example.com
realm = EXAMPLE.COM
security = ads
idmap config * : range = 16777216-33554431
template shell = /bin/bash
kerberos method = secrets only
winbind use default domain = false
winbind offline logon = false
idmap config * : range = 16777216-33554431
passdb backend = tdbsam
winbind enum users = yes
winbind enum groups = yes
strict locking = no
Re: Active directory connection
Posted: 2018/09/24 15:53:10
by robertshatty
I tried below method also and it's working fine here,
https://www.linuxtechi.com/integrate-rh ... directory/
Now tell me how to setup
pam mkhomedir to make homedir on custom path over server for roaming profiles ?